Security Researcher | Full Stack Developer | CTF Player
Pentester with hands-on experience in web application security, vulnerability assessment, and exploit development. Strong defender mindset from SOC/EDR operations. Active on TryHackMe and HackTheBox.

Hi, I'm Max Jensen
Security Researcher & Full Stack Developer
Crafting secure digital experiences while breaking into systems legally. Passionate about offensive security and building robust applications.
Who I Am
A passionate security researcher and full-stack developer with expertise in breaking and building secure systems.
IT Security
Offensive security & pentesting
Full Stack Dev
Modern web applications
Red Team
Attack simulation & assessment
Cryptography
Secure implementations
Security
Frontend
Backend
Tools
CTF Journey
Actively hacking on HackTheBox and TryHackMe. Here's my progress in the offensive security community.
Latest Threats
Real-time security news, advisories, and research from leading cybersecurity sources.
Security News
CVEs & Advisories
Research & Analysis
Key Takeaway
Stay proactive by monitoring these feeds regularly. Subscribe to security advisories for critical software in your environment and prioritize patching based on CVSS scores and active exploitation status.
My Work
A collection of security research projects, tools, and full-stack applications I've built and contributed to.
Autonomous SecOps Platform
AI-Powered Threat Detection & Response
Security operations platform using AI/ML to detect and block 29+ attack types with autonomous decision-making. Features self-learning threat intelligence, adaptive defense mechanisms, and predictive security - engineered for cost-efficiency at $1.50/month.
🚀 Advanced CapabilitiesLatest
Security Analytics Dashboard
Top Attack Types (MITRE ATT&CK)
7-Day Attack Trends
📊 Monthly Overview (Aggregated)
💡 Engineering Highlights
Latest Articles
Writing about security research, development best practices, and lessons learned from CTF challenges.
My Reading Journey
Books that have shaped my understanding of security, development, and personal growth.
Currently Reading

Practical Malware Analysis
by Michael Sikorski
Completed
Recommended Reads

Secrets and Lies
by Bruce Schneier

The Web Application Hacker's Handbook
by Dafydd Stuttard & Marcus Pinto
Favorite Moments
A collection of memorable moments from security research, exploit development, and my journey in cybersecurity.
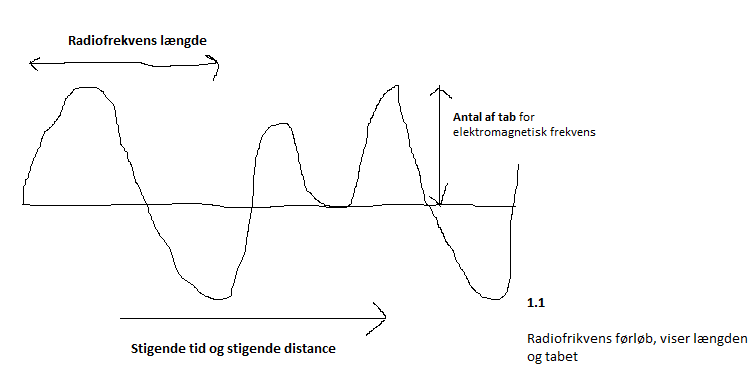
If you want to make some measurements and get a hang on how far your frequencies are reaching, then it's also essential to remember where your pointing is at
1 / 23
What People Say
Recommendations from colleagues, managers, and collaborators I've had the pleasure of working with.
"Jeg har haft fornøjelsen af Max som supporter i Cloud People og kan give ham mine bedste anbefalinger. Max er gået til opgaverne med stort engagement og lyst til at lære nyt, og han har været hurtig til at finde sin plads i teamet. Max har fået løst de givne opgaver på bedste vis, og kundernes tilfredshed er helt sikkert et bevis på, at han har potentiale til meget mere end 1. line support."

Get In Touch
Have a security project in mind, interested in collaboration, or just want to chat? Reach out through any of these channels.
Prefer the fastest response? LinkedIn is the best way to reach me.








